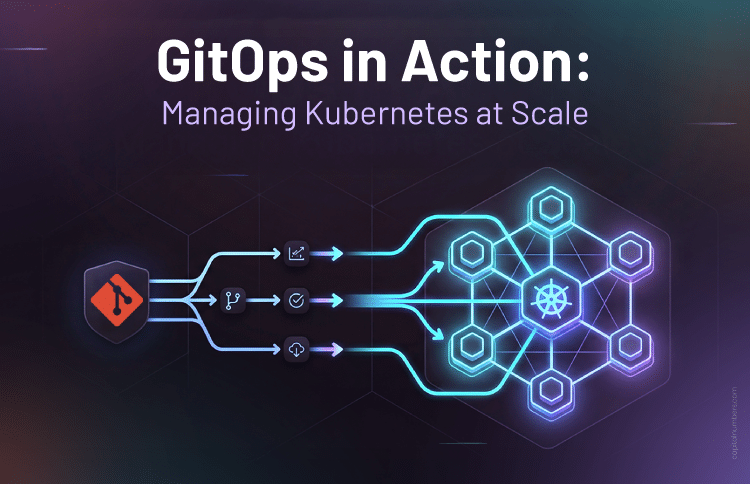
GitOps in Action: Managing Kubernetes at Scale
Table of Contents
Kubernetes has evolved into the backbone of modern digital platforms. Enterprises rely on it to power mission-critical workloads, SaaS platforms, internal developer systems, and globally distributed applications. However, as adoption matures, operational complexity increases dramatically. Managing one cluster may be manageable, but managing multiple clusters across environments, regions, compliance boundaries, and customer segments introduces systemic risk.
As organizations scale, they face a recurring challenge: how to maintain consistency, security, governance, and deployment velocity without introducing operational fragility. Kubernetes provides orchestration, but it does not inherently provide governance discipline. That responsibility falls on operational design.
GitOps addresses this challenge by transforming Kubernetes management from a manually driven process into an automated, declarative, and continuously reconciled system. It shifts operational control from human intervention to version-controlled intent.
GitOps is not simply a deployment pattern – it is an operational discipline. By establishing Git as the single source of truth and enabling automated reconciliation, GitOps transforms Kubernetes from a mutable environment into a deterministic, auditable, and scalable platform.
The Hidden Complexity of Scaling Kubernetes
In early-stage adoption, teams often rely on kubectl-driven workflows. Engineers apply YAML manifests manually, patch deployments during incidents, and adjust configurations directly inside clusters. While workable at a small scale, this model introduces structural weaknesses as systems grow.
At enterprise scale, organizations typically operate multiple clusters for Development, UAT, Production, Disaster Recovery, and regional deployments. Each cluster may include dozens or hundreds of microservices, ingress configurations, RBAC policies, network rules, CI/CD integrations, monitoring stacks, and security controls.
As scale increases, manual operations introduce predictable risks:
- Configuration drift between environments
- Untracked production hotfixes
- Limited rollback confidence during incidents
- Inconsistent policy enforcement
- Audit and compliance traceability gaps
Over time, Dev, UAT, and Production environments begin to diverge subtly. A quick production fix might never be reflected in source control. A manual scaling adjustment may not exist in staging. During a critical incident, teams struggle to determine which configuration truly represents the intended state.
What initially feels flexible eventually becomes fragile. Production instability often results from configuration inconsistencies rather than application defects. This is the tipping point where operational maturity must evolve.
GitOps: From Deployment Pattern to Governance Model
GitOps redefines Kubernetes operations by shifting authority from individuals to systems. Instead of engineers pushing changes directly into clusters, GitOps controllers pull approved changes from version-controlled repositories.
Four foundational principles define GitOps:
- Declarative infrastructure fully defined in code
- Version-controlled repositories with mandatory review workflows
- Automated synchronization via GitOps controllers
- Continuous reconciliation to detect and correct drift
This approach creates a powerful governance layer. Every change flows through a Pull Request. Every deployment is traceable to a commit. Every rollback can be executed through version control. Clusters become predictable systems that reflect approved configuration—not ad-hoc intervention.
By treating infrastructure as code and enforcing PR-driven workflows, GitOps aligns engineering operations with compliance, audit, and executive oversight requirements.
Enterprise GitOps Architecture
A mature GitOps architecture integrates multiple layers including source control, CI pipelines, artifact registries, GitOps controllers such as Argo CD or Flux, Kubernetes clusters, policy engines, and observability platforms.
In a typical enterprise implementation, application code and infrastructure configuration are separated into dedicated repositories. CI pipelines build container images, run automated tests, perform vulnerability scans, and publish artifacts to a secure registry, enabling reliable containerized builds and automated deployment workflows.Once validated, a configuration update—often an image tag change—is submitted via Pull Request to the GitOps repository.
The reconciliation loop forms the core of the system. Controllers continuously compare the live cluster state against the desired state stored in Git. If divergence occurs—whether due to manual intervention or system anomaly – the controller automatically restores the declared configuration.
This closed-loop automation dramatically reduces configuration drift, improves mean time to recovery (MTTR), and increases overall deployment confidence.
Multi-Cluster and Multi-Region Strategy
Large enterprises often operate clusters across multiple regions for latency optimization and disaster resilience. Clusters may also be isolated per customer, compliance boundary, or product line.
GitOps enables standardized cluster bootstrapping. A new cluster can be provisioned using infrastructure-as-code tools such as Terraform. Once the GitOps controller is installed and connected to the repository, applications, ingress configurations, policies, and monitoring stacks are automatically synchronized.
This model ensures that every cluster – regardless of region or purpose—conforms to the same baseline architecture, security standards, and operational practices.
Security, Compliance, and Risk Mitigation
From an executive standpoint, GitOps aligns directly with governance requirements. Every infrastructure change is traceable to a commit, a Pull Request, and an approval workflow.
Security controls are strengthened through:
- Policy-as-code enforcement using OPA or Kyverno
- Encrypted secrets management (Sealed Secrets, SOPS, Vault)
- Elimination of direct production access
- Automated compliance validation in CI pipelines
This structured model improves compliance readiness for frameworks such as SOC2 and ISO 27001, while reducing insider risk and configuration-related vulnerabilities.
Disaster Recovery and Business Continuity
Traditional disaster recovery relies on restoring backups and manually reconstructing infrastructure. GitOps treats infrastructure as reproducible code.
In the event of cluster failure, the recovery workflow becomes deterministic:
- Provision new infrastructure
- Install GitOps controller
- Connect to repository
- Allow automated reconciliation to rebuild full system state
This approach significantly improves Recovery Time Objectives (RTO), simplifies disaster recovery testing, and enhances organizational resilience.
Business Impact and Strategic Value
Organizations adopting GitOps frequently observe measurable improvements including reduced incident frequency, faster rollback capability, improved deployment velocity, and stronger audit posture.
Beyond metrics, GitOps drives cultural transformation. Teams move from reactive troubleshooting to proactive engineering discipline. Operations become predictable. Deployments become repeatable. Governance becomes embedded within the workflow rather than layered on afterward.
Ultimately, GitOps allows enterprises to scale Kubernetes environments with confidence – balancing innovation speed with operational stability.
Conclusion
Managing Kubernetes at scale demands automation, governance, security, and operational discipline supported by mature DevOps services and automation solutions. Kubernetes alone provides orchestration – but not operational maturity.
GitOps unifies these dimensions into a cohesive operational model. It transforms clusters from mutable systems into declarative platforms. It replaces ad-hoc intervention with structured workflows. It embeds compliance into engineering practice.
For enterprises operating distributed, cloud-native systems, GitOps is not merely an optimization – it is a strategic enabler of scalable, secure, and reliable platform operations.